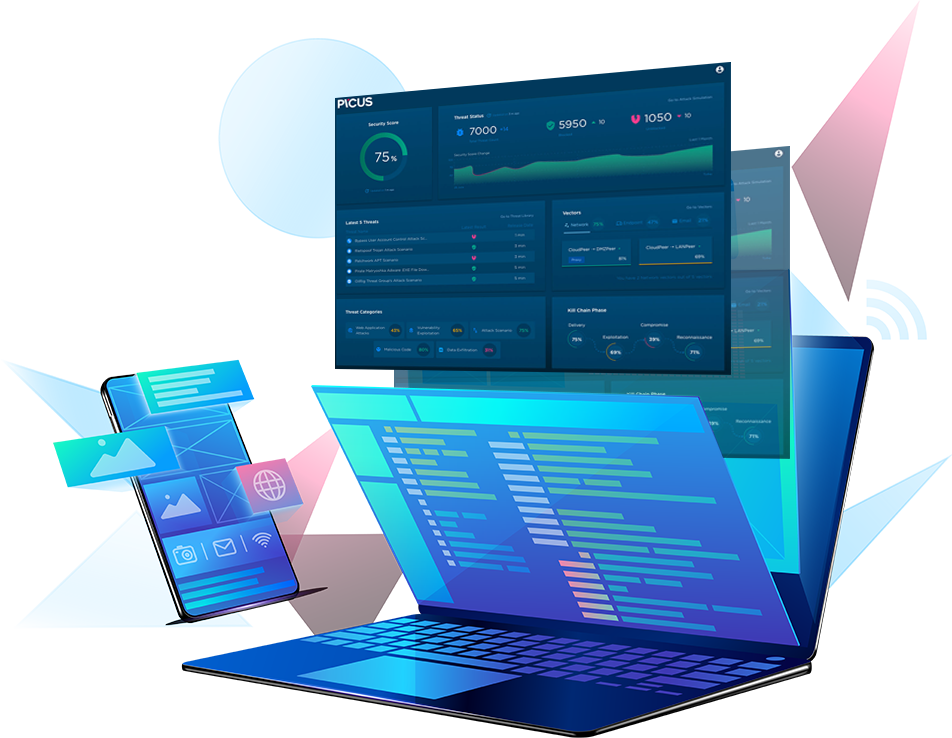
Picus Security is a breach and attack simulation (BAS) vendor. BAS was categorized as a new security assessment domain in 2018 by Gartner, and Picus has been named as a Cool Vendor in 2019.
Picus is an intelligence-driven security validation platform that simplifies security operations and optimizes defencesThe platform safely emulates cyber threats and provides mitigation guidance – allowing organizations to improve visibility and security investment utilization..
Security Control Validation and Mitigation
Threat-centric, pervasive, flexible end-to-end security validation.
Picus Security Control Validation and Mitigation is a threat-centric, flexible platform that allows you to measure security effectiveness and quickly assess controls. The platform is driven by a large Threat Library managed by Picus Labs, as well as a comprehensive set of mitigation recommendations from the Picus Technology Alliance Network. It automatically and consistently identifies gaps, and instantly applies selected mitigation advice for security validation, hardening, and mitigation.

How it works
The Picus Security Control Validation and Mitigation solution consists of Picus Threat Library, Threat Emulation Module, and Mitigation Library. While the Threat Emulation Module continually collects adversarial content from the Threat Library and runs assessments, the Mitigation Library reveals available signatures and policies developed by the vendors to address the identified security control gaps.

Detection Analytics and Mitigation
Continuous security validation and that boosts detection effectiveness.
Picus Detection Analytics & Mitigation is a threat-centric, multi-component solution based on Picus Threat Library, Detection Analytics Module and Mitigation Library. The solution offers easy-to-implement mitigation suggestions and updates, improving SOC processes across the board – from threat intelligence to incident analysis and incident response. It’s designed to make data collection and analytics tasks more efficient and streamlined.